Every device that connects to a network whether it’s your smartphone, laptop, smart TV, or even a refrigerator has a unique fingerprint embedded in its hardware. This fingerprint is called a Media Access Control (MAC) address. Unlike IP addresses that can change depending on the network, a MAC address is permanently assigned by the manufacturer and burned into the device’s network interface card (NIC). Understanding how a MAC lookup works is essential for network administrators, cybersecurity professionals, and anyone curious about how devices are uniquely identified in the digital world.
When you perform a MAC lookup, you’re essentially translating the first half of that 48-bit address into the name of the company that made the device. This process relies on a globally maintained database managed by the IEEE, revealing the manufacturer (known as the Organizationally Unique Identifier or OUI) and sometimes even the specific model range. While it won’t tell you the exact serial number or owner, it provides immediate context about what kind of device is on your network.
What Is a MAC Address and Why Is It Unique?
A Media Access Control address is a 48-bit hexadecimal identifier written as six pairs of characters separated by colons or dashes (for example, 00:1A:2B:3C:4D:5E). The first 24 bits (three octets) represent the Organizationally Unique Identifier assigned exclusively to a single manufacturer by the IEEE. The remaining 24 bits are assigned by that manufacturer to ensure every network card they produce is globally unique. No two devices in the world are supposed to share the same MAC address under normal circumstances. This permanence and uniqueness make MAC addresses the most reliable way to identify hardware at Layer 2 of the OSI model.
Structure of a MAC Address
Most MAC addresses today use the EUI-48 format, though modern devices are slowly transitioning to EUI-64. The second bit of the first octet indicates whether the address is universally administered (0) or locally administered (1). Universally administered addresses are the standard ones assigned by manufacturers during production. Locally administered addresses are manually overridden by users or software, often for privacy or virtualization purposes. Understanding this structure is the foundation for performing accurate lookups.
Difference Between MAC and IP Addresses
IP addresses are logical and assigned by networks, while MAC addresses are physical and burned into hardware. An IP address can change every time you connect to a new Wi-Fi, but the MAC stays the same. Routers use MAC addresses to deliver data within a local network (ARP process), while IP handles routing across the internet. Because of this, MAC addresses are crucial for local network security and device tracking. Many people confuse the two, but they serve completely different layers of networking.
Unicast vs Multicast MAC Addresses
Unicast addresses (first octet’s least significant bit = 0) are meant for one specific device. Multicast addresses (bit = 1) are used for sending data to groups, such as in IPTV or discovery protocols. Broadcast address FF:FF:FF:FF:FF:FF is a special multicast used to reach every device on the local network. Lookup tools usually focus on unicast addresses since those reveal manufacturers. Knowing the type helps interpret lookup results correctly.
How Is the Global MAC Database Maintained?
The Institute of Electrical and Electronics Engineers (IEEE) owns and operates the official registry of OUIs. Manufacturers pay a fee to receive blocks of 16 million addresses (24 bits) identified by a unique 24-bit prefix. Large companies like Apple, Samsung, and Cisco own multiple OUIs because they produce billions of devices. The public portion of this registry is freely downloadable and updated daily. Third-party websites and tools simply mirror or cache this official list for faster lookups.
Role of the IEEE Registration Authority
IEEE acts as the single source of truth to prevent address collisions worldwide. They assign OUI-36, MA-L (Medium), MA-M (Small), and traditional MA-L (Large) blocks. Applications are reviewed to ensure only legitimate hardware manufacturers receive assignments. Publicly searchable registries include company name, address, and assignment date. This centralized system has worked reliably since the 1980s.
Public vs Private OUI Lists
The full official list is available as a plain text file on the IEEE website without login. Many commercial tools add private databases of common randomized or virtual MAC prefixes. Some vendors (notably Apple and Microsoft) use private ranges for privacy features. Free online lookup sites usually combine IEEE data with crowdsourced additions. Always prefer tools that cite the latest IEEE data for maximum accuracy.
How Often the Database Updates
IEEE updates the public registry multiple times per week as new assignments are approved. Major lookup services automatically sync within 24–48 hours of changes. New IoT and automotive manufacturers are the fastest-growing applicants. Historical assignments remain valid forever unless a company goes bankrupt and the block is reclaimed. Staying current matters when identifying very new devices.
How Does a MAC Lookup Actually Work?
When you enter a MAC address into a lookup tool, the software extracts the first three octets (OUI). It then searches its local or online copy of the IEEE registry for an exact match. If found, it returns the registered organization name and sometimes country of registration. The process usually completes in under one second even on free websites. Advanced tools may also check secondary databases for device model hints.
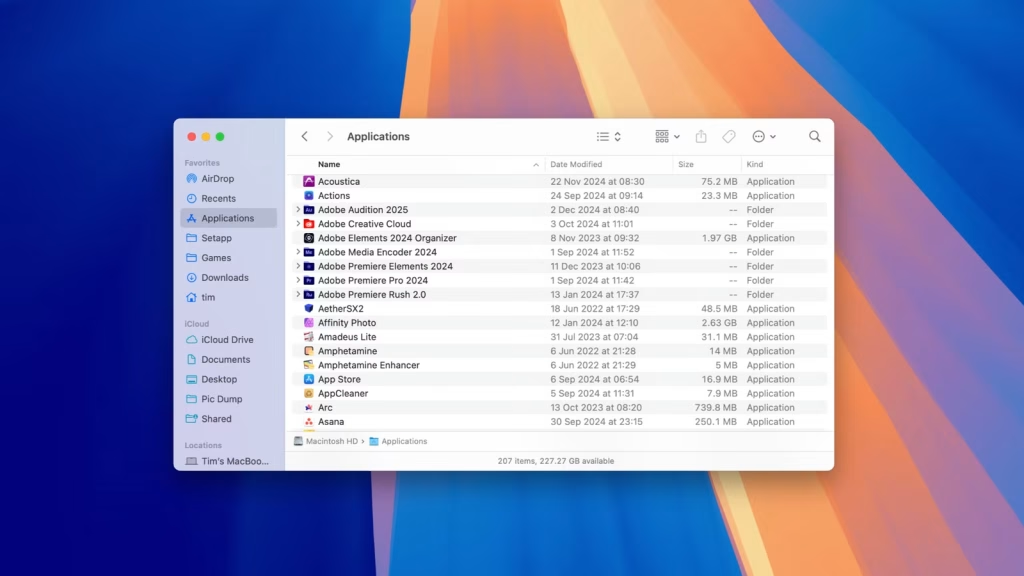
Lookup Process
- User pastes or types a full MAC address (with or without separators).
- Tool normalizes format and validates it’s 48 bits and hexadecimal.
- First 24 bits are isolated and searched against the OUI database.
- Matching record returns vendor name, block size, and assignment details.
- Result is displayed instantly with optional copy or export features.
Popular Free MAC Lookup Tools
- IEEE official search (standards.ieee.org/products-services/regauth/oui)
- Wireshark’s built-in OUI lookup (most accurate offline option)
- macvendors.com, maclookup.app, and dnschecker.org/mac-lookup
- Browser extensions like “MAC Address Lookup” for instant selection lookups
- Command-line tools such as maclookup (Python) or arp-scan
API Services for Developers
Many sites offer free-tier APIs returning JSON with vendor data. Paid services provide higher rate limits and historical change tracking. Integration is common in network monitoring platforms like Zabbix and PRTG. Some APIs enrich results with device type (phone, laptop, IoT) using crowdsourced data. Always check terms of service for commercial use restrictions.
Limitations of MAC Address Lookups
MAC addresses can be spoofed in seconds using tools like macchanger or from within Windows Device Manager. Randomized MAC addresses rotate regularly for privacy. Virtual machines and containers often generate temporary local MACs starting with 00:00:00 or 02:xx:xx. Some manufacturers reuse OUIs across vastly different product lines. Therefore, a lookup only confirms possible manufacturer, never definitive identity.
MAC Randomization and Privacy Features
Modern phones and laptops present a different MAC to each Wi-Fi network. This breaks traditional tracking used by retail stores and marketing companies. Randomized addresses usually set the second bit to 1 (locally administered). Lookup tools will either return “private” or no result at all. Enterprise Wi-Fi systems can force devices to use real MACs via policy.
Spoofing and Security Implications
Attackers routinely spoof legitimate MACs to bypass MAC filtering on routers. Network administrators must combine MAC allow-lists with certificate or 802.1X authentication. Forensic investigators treat MAC evidence as circumstantial because of easy spoofing. However, most consumer devices never change their real burned-in address. Balance convenience and security accordingly.
When a Lookup Returns “Unknown”
New manufacturers or very recent OUI assignments may not yet appear in third-party databases. Some Chinese OEM factories use unregistered or borrowed OUIs. Virtualization platforms (VMware, Hyper-V) generate predictable local ranges. IoT devices from obscure brands frequently fall into this category. Wait a few days or check the official IEEE list directly.
Real-World Applications of MAC Lookups
Network administrators use MAC lookups daily to identify mystery devices consuming bandwidth. Parents can spot unauthorized phones or gaming consoles on home networks. Cybersecurity teams detect hardware from sanctioned countries or known bad actors. Retail IT blocks entire vendors. Even coffee shops use it to limit connections from virtual machines abusing guest Wi-Fi.
Home Network Security and Parental Control
Modern routers (ASUS, Netgear, TP-Link) show vendor directly in the client list. You can block all devices from certain manufacturers with one click. Identify that “Xiaomi Communications” device that appeared at 2 a.m. Combine with traffic monitoring to catch crypto-mining IoT bulbs. Simple five-minute audit can dramatically improve home security.
Enterprise Asset Management
Large companies track laptops, printers, and VoIP phones by MAC in CMDBs. Automated scripts flag when a non-approved vendor appears on the network. Help desks resolve tickets faster knowing it’s a 2024 MacBook versus 2015 Dell. Integration with NAC (Network Access Control) solutions like Cisco ISE or Aruba ClearPass. Saves thousands of man-hours annually in medium to large organizations.
Digital Forensics and Law Enforcement
Investigators recover MAC addresses from router logs and access point memory. Even if the device is offline, the vendor provides investigative leads. Combined with cell tower data, can place a specific phone brand at a crime scene. Courts accept MAC evidence when chain of custody is properly documented. Always paired with other digital footprints for stronger cases.
Future of Device Identification Beyond MAC
IEEE is slowly depleting the 16 million possible OUIs, pushing adoption of 64-bit EUI-64 addresses. Privacy regulations (GDPR, CCPA) accelerate the shift to randomization and ephemeral identifiers. Cryptographic device attestation (like Apple’s Private Access Tokens) may replace MAC entirely. Zero-trust networks increasingly ignore MAC in favor of certificate-based identity. Yet for the foreseeable future, MAC lookup remains a quick, universal tool.
Rise of EUI-64 and New Formats
EUI-64 inserts FF:FE between OUI and device portion for IPv6 auto-configuration. Some 5G and automotive devices already ship with 64-bit identifiers. Lookup tools are being updated to handle both formats seamlessly. Backward compatibility ensures old EUI-48 addresses keep working. Transition will take another decade or more.
Privacy-Enhancing Technologies
Apple’s iCloud Private Relay and Android Private Compute Core hide real hardware identifiers. Wi-Fi Alliance’s Enhanced Open and WPA3 encourage address rotation. Future routers may never log real MAC addresses by default. Users gain privacy, but network troubleshooting becomes harder. Balance continues to shift toward individual control.
Alternative Identification Methods
Device fingerprinting using browser or protocol behavior is gaining traction. Manufacturer Usage Description (MUD) files let IoT devices declare expected traffic patterns. Bluetooth Low Energy also uses rotatable addresses with similar privacy goals. Combining multiple signals will replace single-point MAC identification. The era of simple vendor lookup is evolving rapidly.
Conclusion
In summary, MAC lookup remains one of the fastest and most accessible ways to identify the manufacturer of almost any networked device, relying on a robust global standards maintained by the IEEE for over four decades. While privacy features and spoofing limit its forensic certainty, everyday administrators, security professionals, and curious users continue to benefit from its simplicity and universality.